About the Project
Welcome back, tech enthusiasts! Today, I'm excited to introduce ARPoLan, a project that started as an experiment to explore the potential of combining the Arduino Pro Micro and the W5500 Ethernet module. This powerful device can perform network scanning, ARP spoofing, and even act as a local Rubber Ducky. Let me take you through building and testing this network security tool.
Features & Components
ARPoLan combines several powerful components to deliver its impressive capabilities:
- Network Scanning: Discover devices on the local network by sending ARP requests and collecting responses.
- ARP Spoofing: Perform ARP spoofing attacks to intercept and manipulate network traffic.
- HID Functionality: Utilize the Atmega32u4's USB HID capabilities for additional attack vectors.
- Real-time Monitoring: Visual and serial indicators for attack detection and network activity.
Getting Started
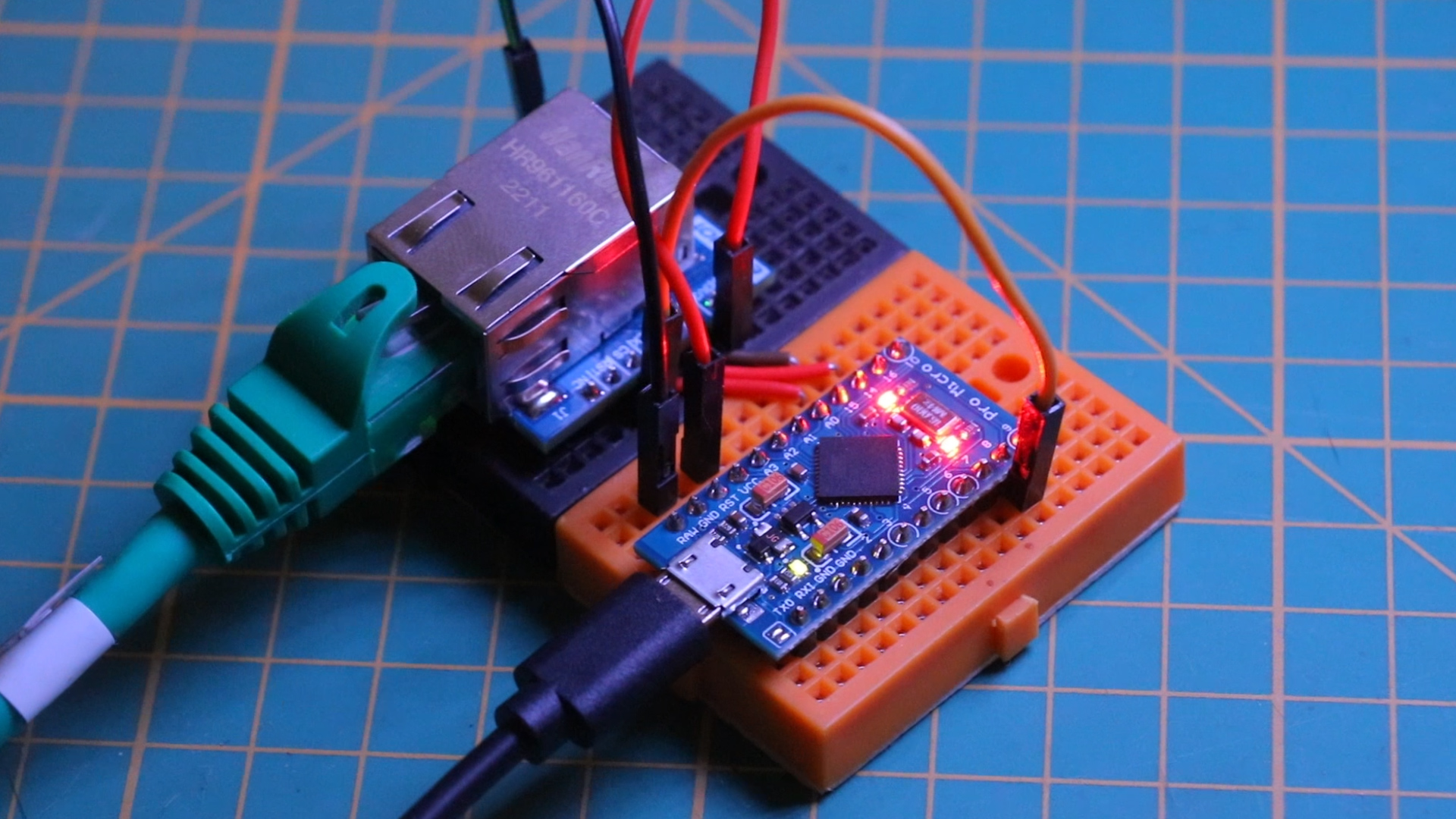
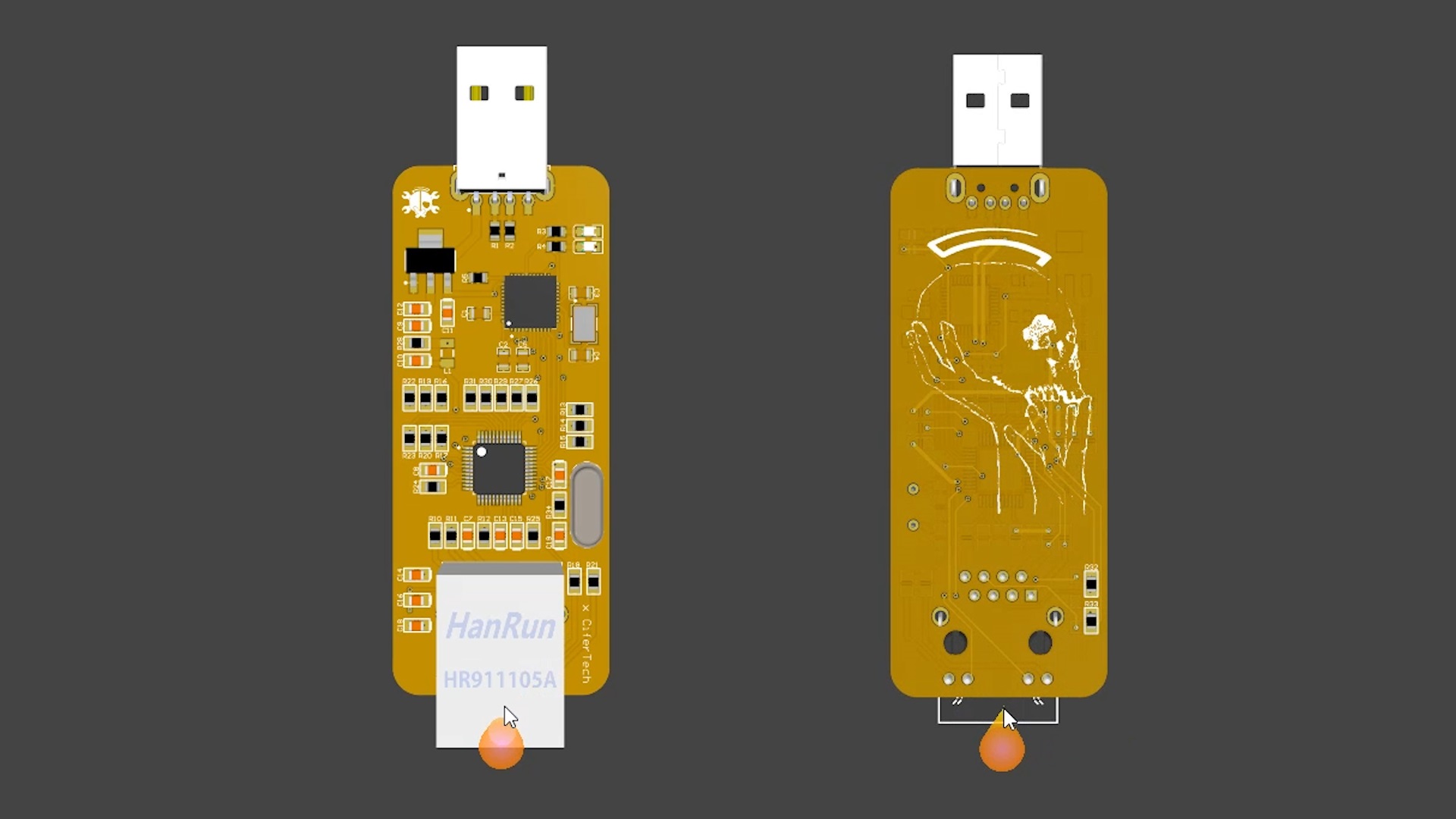
I designed the PCB for ARPoLan using Altium Designer, creating a simple yet efficient two-layer layout. Here’s a breakdown of the components used:
- Atmega32u4 Microcontroller: Handles USB communication and processing tasks.
- W5500 Ethernet Module: Provides reliable network connectivity with an integrated hardware TCP/IP stack.
- 25 MHz Crystal Oscillator: Ensures precise timing for network operations.
- RJ45 Ethernet Socket: Facilitates network connections with integrated status LEDs.
- LM1117 Voltage Regulator: Supplies a stable 3.3V power to the W5500.
- USB A Port: Allows for easy programming and data transfer.
- Passive Components: Capacitors and resistors for power stabilization and signal integrity.
The communication between the W5500 and the Atmega32u4 is handled via the SPI protocol, ensuring quick and reliable data transfer.
Schematic
The PCB for ARPoLan was designed using Altium Designer, featuring a two-layer layout optimized for compactness and efficiency. The board integrates all necessary components, ensuring reliable connections between the Atmega32u4 and the W5500.

Connection Table
- The SS (Slave Select) pin can be connected to any digital pin on the Arduino Pro Micro, but it must be defined correctly in the code.
- Make sure the GND of the Arduino Pro Micro is connected to the GND of the W5500 module to ensure a common ground.
- This setup will enable SPI communication between the Arduino Pro Micro and the W5500 Ethernet module.
Usage
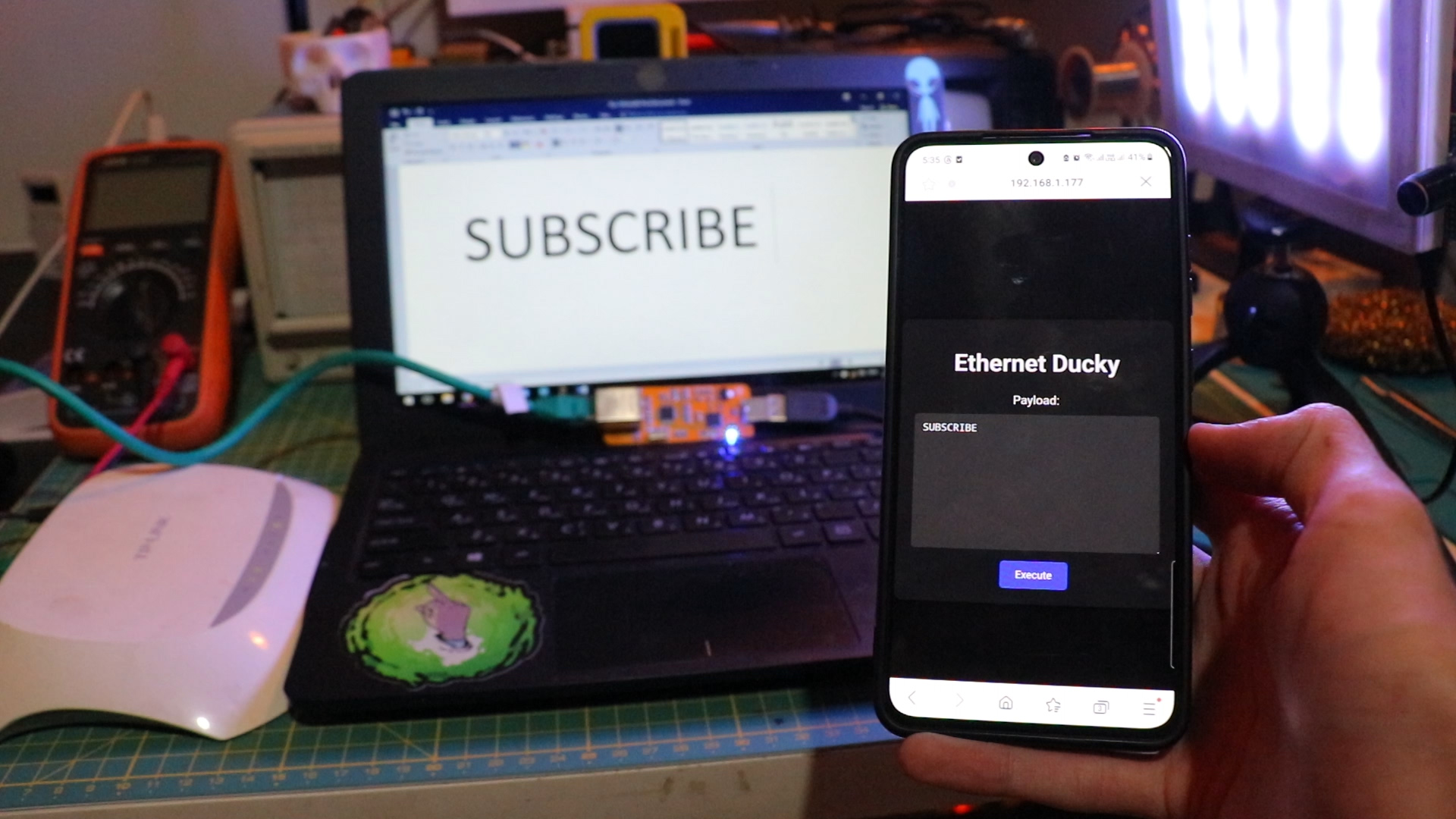
First Code: Local Rubber Ducky The first piece of code transforms ARPoLan into a local Rubber Ducky. The Atmega32u4's USB HID capabilities allow it to act like a keyboard or mouse, injecting pre-programmed keystrokes into a connected computer. This was a fun experiment, though I refer to it as the "bad idea" code due to its potential risks.
Second Code: ARP Spoofing Next, I tested the ARP spoofing code. This script injects malicious ARP packets into the network, leveraging the processing power of the Atmega32u4 and the network capabilities of the W5500. While not overly powerful, it demonstrated the device's potential for network security tasks.
Third Code: Network Scanning The final code was for network scanning. By sending ARP requests to all IP addresses within a specified range, ARPoLan could identify active devices on the network. This functionality is crucial for network monitoring and penetration testing.
EXPANDED TECHNICAL DETAILS: Network Scanning & Forensics
The core scanning functionality of ARPoLan is a powerful network forensics tool. It operates by executing a systematic sweep across the local subnet to discover every connected device.
The Ping-Sweep Traversal Algorithm: The code doesn't just ping one address. It iterates through a range, typically 1 to 254 for a standard /24 subnet. For each IP address in that range, it sends an Address Resolution Protocol (ARP) request. Any device that is active and on the network will respond with its MAC address, allowing the tool to catalog it. This process can scour an entire subnet in under a minute, revealing hidden smartphones, IoT devices, or unauthorized computers.
// Example conceptual loop for network scanning
for (int i = 1; i <= 254; i++) {
IPAddress targetIP(192, 168, 1, i);
sendARPRequest(targetIP); // Send an ARP "Who has this IP?" request
if (checkForARPResponse()) {
logDevice(targetIP, respondingMAC); // Catalog the discovered device
}
}
Spoofing and The Alerting Failsafe: Beyond simple discovery, the tool can be configured for active monitoring. A "Known Device" registry can be hard-coded or learned. When a scan detects a new, unknown MAC address (like `192.168.1.48`), it can trigger an alert. This alert could be a visual indicator on the device itself, a serial log, or even an external notification via a webhook to services like Telegram or IFTTT, instantly informing the network administrator of a potential intruder.
Cyber Forensics Loadout Considerations: While this project uses an Atmega32u4 with a W5500 for a wired, stealthy approach, similar functionality can be achieved with Wi-Fi chips like the ESP8266 or ESP32 for wireless sweeps. Adding a display, like a small OLED, provides real-time visibility into the discovered IP address tables.
Code & PCB
If you're interested in building this project, the code and schematic are available on GitHub. Simply visit the GitHub repository to download the necessary files. If the project gains attention, I’ll open-source the PCB files as well. Feel free to test the code and share your feedback or improvements.
GitHub repository: github.com/cifertech/arpolan
Conclusion
Creating ARPoLan was a fascinating journey into network security and hardware integration. From designing the PCB to writing and testing the code, this project showcased the potential of combining simple yet powerful components to achieve sophisticated functionalities. Stay tuned for future updates and enhancements, and don’t forget to check out the project details on my GitHub. If you have any ideas or suggestions, I would love to hear them!